Mobile Platform Security and Privacy Standards
Modern mobile devices act as the primary gateway to our personal and professional lives, making the choice between operating systems a significant decision for many users. Understanding how different platforms handle sensitive information is crucial for maintaining digital safety in an increasingly connected world.
The evolution of mobile technology has transformed the way individuals interact with the world, shifting from simple communication tools to complex pocket-sized computers. As these devices store an increasing amount of sensitive personal data, from financial records to private communications, the underlying security architecture of the operating system becomes the most critical factor in protecting user privacy and ensuring long-term digital safety. Choosing between different platforms often involves evaluating how each environment manages data access and mitigates external threats.
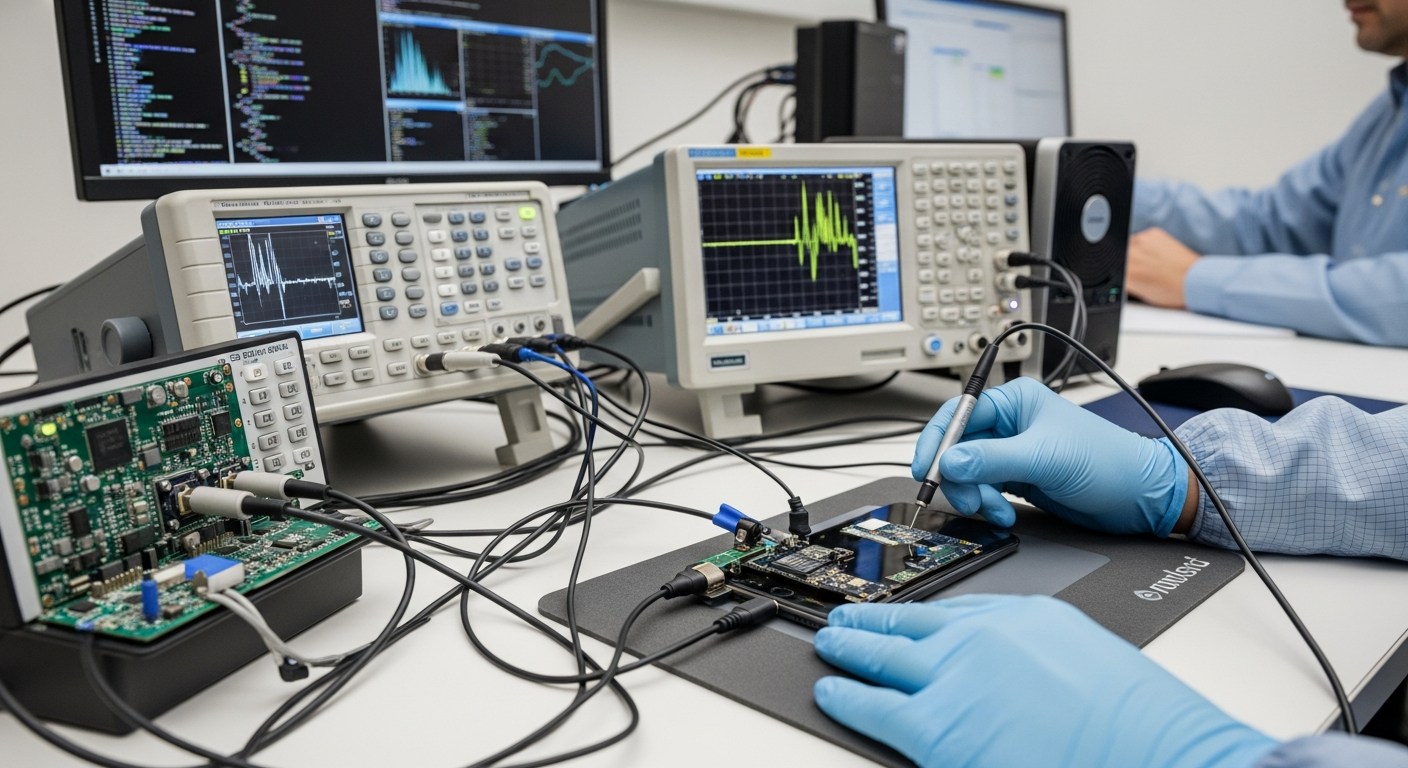
Security and Hardware Integration
Modern smartphone security begins at the physical level, where hardware components are designed to create a trusted execution environment. Both major mobile ecosystems utilize dedicated security chips, such as the Titan M series or the Secure Enclave, to handle cryptographic keys and biometric data separately from the main processor. This hardware-level isolation ensures that even if the primary software environment is compromised, the most sensitive credentials remain protected. Furthermore, the integration of verified boot processes ensures that only authorized firmware can run on the device, preventing the execution of malicious code during the startup phase.
Software and Firmware Updates
Maintaining the integrity of mobile software requires a consistent and timely distribution of firmware updates. One of the primary differences between mobile platforms lies in how these updates are delivered to the end-user. Centralized systems often benefit from immediate deployment across all compatible devices, whereas fragmented ecosystems may experience delays as updates move through various manufacturers and cellular carriers. Frequent security patches are essential for addressing newly discovered vulnerabilities, and the length of supported software lifecycles has become a key benchmark for evaluating the long-term viability of a device in a professional or personal capacity.
When comparing the leading mobile platforms, it is important to consider the various hardware options and the security features they provide. Different manufacturers offer distinct approaches to privacy, ranging from proprietary encryption methods to hardened kernels designed for enterprise use. Below is a comparison of common devices and their associated security standards.
| Product/Service Name | Provider | Key Security Features | Cost Estimation |
|---|---|---|---|
| iPhone 15 Series | Apple | FaceID, Secure Enclave, App Tracking Transparency | $799 - $1,199 |
| Pixel 8 Series | Titan M2 Security Chip, VPN by Google, 7-year updates | $699 - $999 | |
| Galaxy S24 Series | Samsung | Samsung Knox, Secure Folder, Auto Blocker | $799 - $1,299 |
Prices, rates, or cost estimates mentioned in this article are based on the latest available information but may change over time. Independent research is advised before making financial decisions.
Application Ecosystem and Platform Privacy
The application ecosystem plays a vital role in the overall safety of a mobile platform. Each digital storefront employs different vetting processes to screen for malware and privacy violations before an application is made available to the public. Some platforms enforce strict sandboxing rules, which prevent one app from accessing the data of another without explicit user permission. The debate between curated environments and more open platforms often centers on the balance between user freedom and the risk of sideloading unauthorized software, which can bypass standard security protocols and expose the device to malicious activity.
Interface Usability and Digital Privacy
User interface design significantly impacts how effectively a person can manage their digital privacy. Modern operating systems have introduced comprehensive privacy dashboards that provide a clear overview of which applications have accessed the camera, microphone, or location data. Usability in this context means making complex security settings accessible to the average user, allowing for granular control over permissions. By simplifying the way users interact with their privacy settings, platform developers can ensure that security features are actually utilized rather than ignored due to complexity, thereby strengthening the overall defense of the device.
Telephony and Computing Standards
As mobile devices function as primary computing hubs, they must adhere to rigorous telephony and data transmission standards to protect communication. This includes the implementation of end-to-end encryption for messaging services and the use of secure protocols for voice-over-LTE and data roaming. The convergence of traditional telephony with advanced computing power means that mobile platforms are now subject to the same types of threats as desktop systems, requiring robust firewalls and network monitoring tools. Standardizing these technologies ensures that regardless of the specific hardware used, the underlying communication remains confidential and resistant to interception by unauthorized parties.
In conclusion, the decision between mobile platforms involves a careful assessment of how hardware and software work together to protect user data. While different ecosystems offer unique advantages in terms of update speed, application variety, and interface design, the fundamental goal remains the same: providing a secure environment for digital interaction. By staying informed about the security standards of their chosen platform, users can better navigate the complexities of the modern digital landscape and protect their personal information from evolving threats.